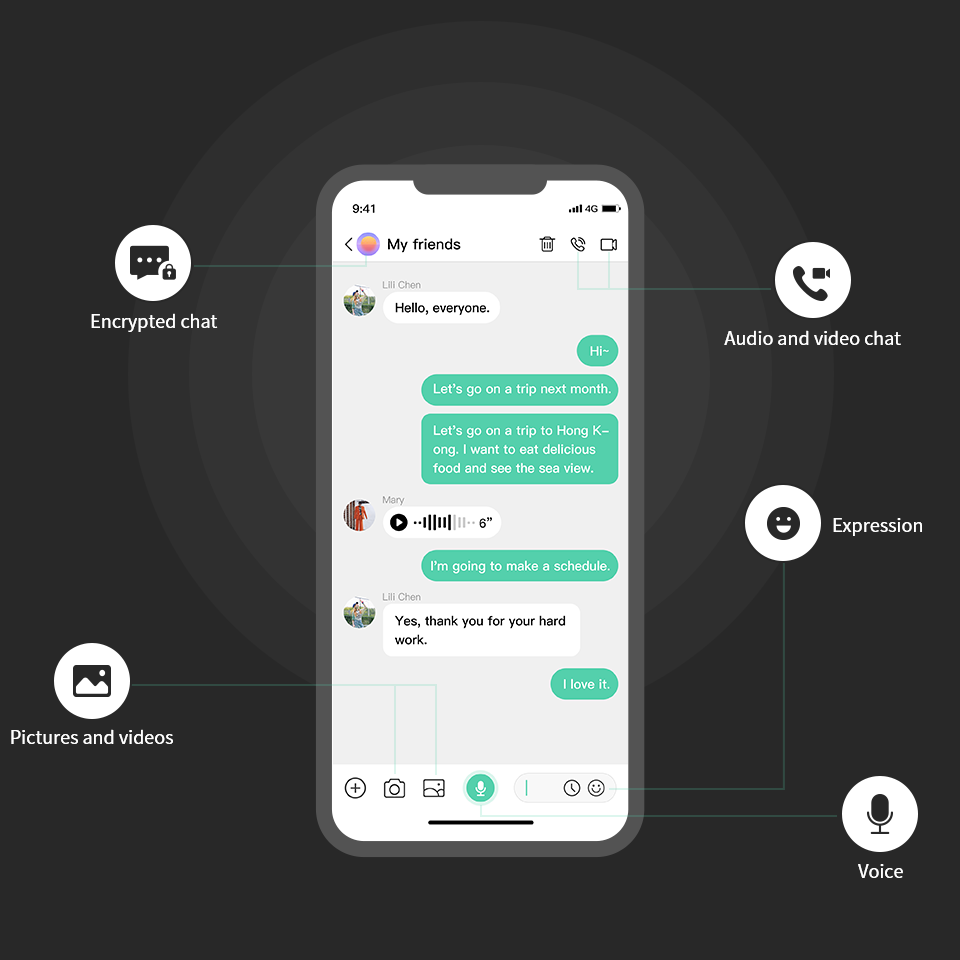
Wireless encrypted voice, video, messaging, file sharing between
users. Make sure your conversations are 100% private and that you are
only linked to the intended party.
All encryption is done on the device, no one can listen.
Technology Introduction

Privacy Protection
We create apps that allow people to communicate freely without
compromising privacy.
We have no access to any of your communications, and our
end-to-end encrypted infrastructure ensures that any
communications over our network remain private and accessible
only to you and your contacts.
We do not require personal information to register for an
account, such as email, phone number or name. We will not
collect any information without your consent.
Information Security Assurance
We use the most secure way to encrypt messages, using the double-gear algorithm for key exchange, which combines double-ratchet, pre-key and cubic elliptic curve Diffie-Hellman key exchange (3-DH), and Use Curve25519, AES-256 and HMAC-SHA256 algorithms as cryptographic primitives primitive). All encryption is done on your device. You have the keys and no one can listen, not even us. Entire communications—including group messages, photos and videos, files, voice calls, and even status messages—are always end-to-end encrypted. Unlike traditional messenger apps, the design excludes fallbacks for unencrypted connections.

Privacy Protection
We create apps that allow people to communicate freely without compromising privacy. We have no access to any of your communications, and our end-to-end encrypted infrastructure ensures that any communications over our network remain private and accessible only to you and your contacts. We do not require personal information to register for an account, such as email, phone number or name. We will not collect any information without your consent.

Security and Privacy
 Chatsafe |  信号 |  telegram |  | |
|---|---|---|---|---|
| Privacy by design: no phone number or email address required The service can be used anonymously | ||||
| End-to-end encryption of transmitted messages No one but the intended recipient can read the chat messages, including us | ||||
| Impossible to circumvent end-to-end encryption End-to-end encryption cannot be circumvented by an unencrypted copy of the message on the device, and there is no fingerprint and state capability on the server side. | ||||
| Service runs its own server Service provider operates and runs all servers, no cloud or hosting services involved | ||||
| Do not use user data for advertising purposes User data is not used for targeted advertising or other marketing purposes | ||||
| No need to access address book No need to grant access to address book to use service (no workarounds/restrictions) |

